Is the Raspberry Pi suitable and safe to host a x.509 certificate authority created with OpenSSL – Random notes of a SysAdmin

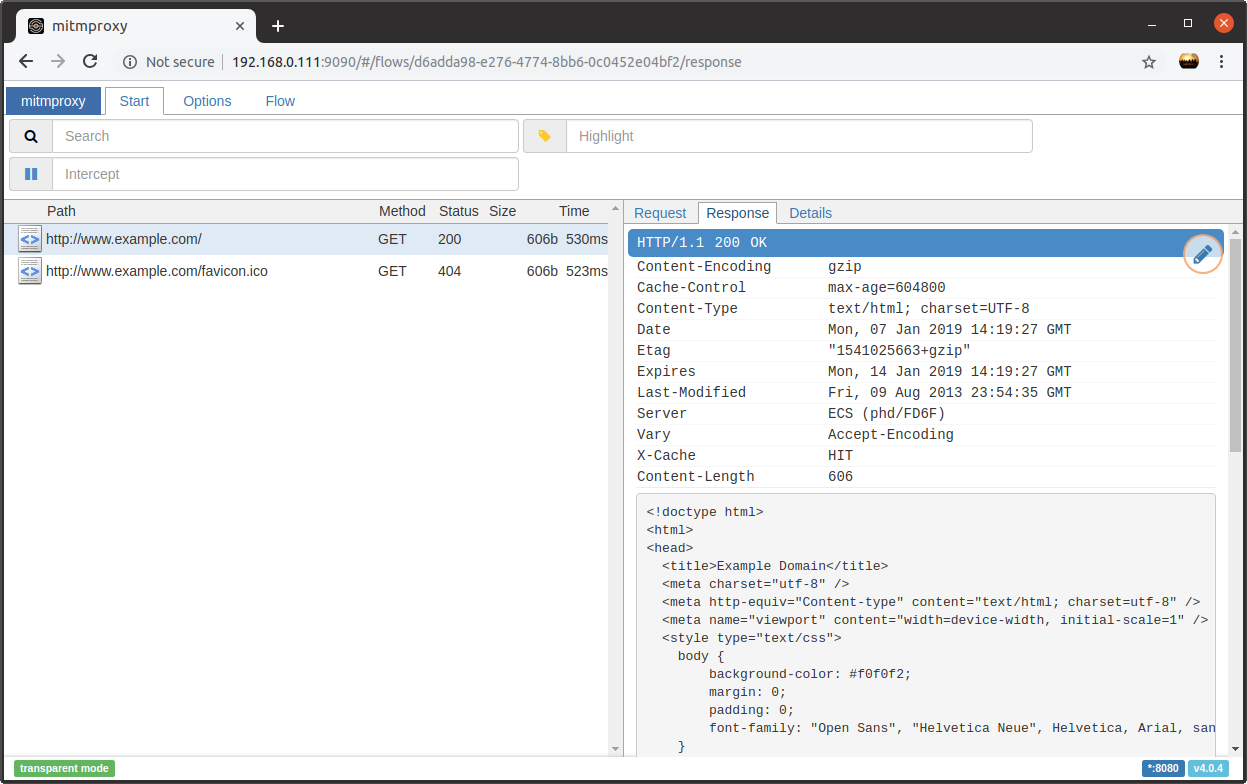
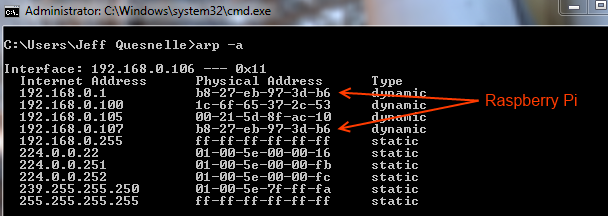
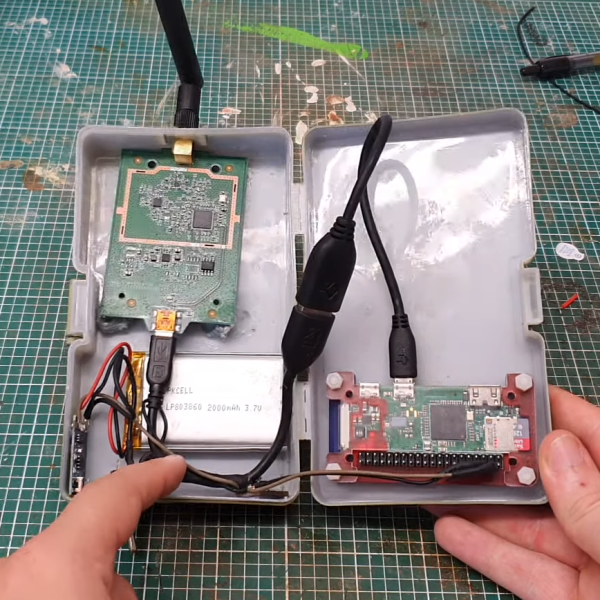
How to Build a Pumpkin Pi — The Rogue AP & MITM Framework That Fits in Your Pocket « Null Byte :: WonderHowTo

How to Build a Pumpkin Pi — The Rogue AP & MITM Framework That Fits in Your Pocket « Null Byte :: WonderHowTo

RaspberryPi – How to solve the SSH warning: WARNING: REMOTE HOST IDENTIFICATION HAS CHANGED! – El Bruno

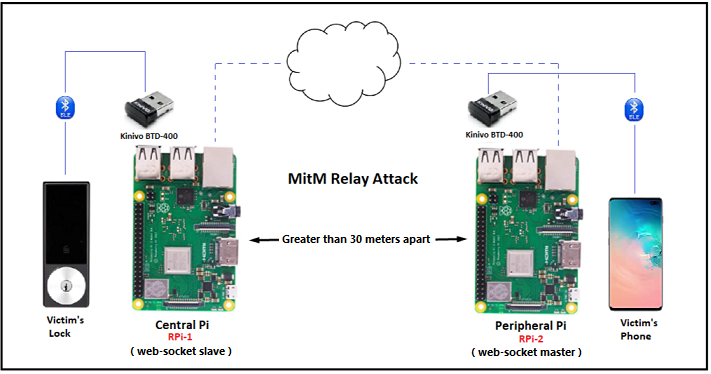
The MitM devices used in this paper. Top: Three 1Gbps Ethernet switches... | Download Scientific Diagram

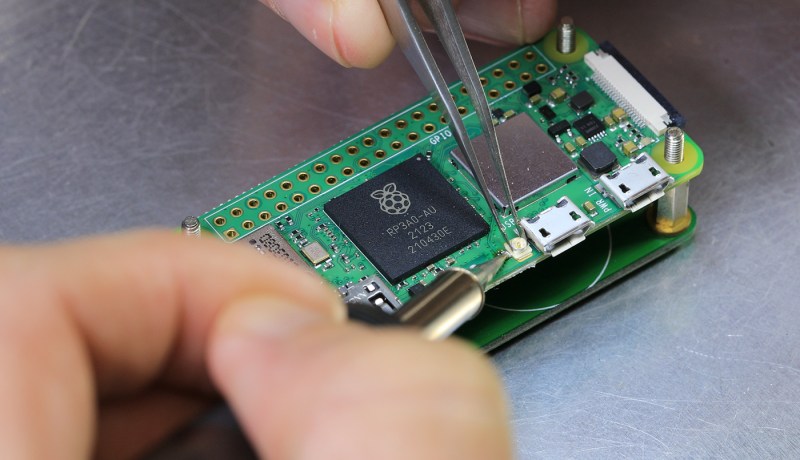
How to Build a Pumpkin Pi — The Rogue AP & MITM Framework That Fits in Your Pocket « Null Byte :: WonderHowTo

Penetration Testing with Raspberry Pi: Muniz, Joseph, Lakhani, Aamir: 9781784396435: Amazon.com: Books